Only a person of the federal government’s premier agencies has absolutely applied the Australian Alerts Directorate’s essential 8 to some of its most critical methods, the national auditor has uncovered.
The obtaining is contained in the 2019 interim financial controls audit of big entities, which reviewed the implementation of the controls now thought of the baseline for cyber resilience.
The Australian National Audit Office’s evaluate focused on the financial and HR methods of 18 agencies, together with Defence, Solutions Australia, Residence Affairs and the Tax Business.
“The evaluate was carried out to confirm the accuracy of reporting and identity cyber security pitfalls that could effects on the planning of financial statements,” the auditor explained [pdf].
“The evaluate consisted of evaluation of coverage and procedural documentation, testing of mitigation methods precise to the FMIS and HRMIS, benefits of sprint assessments and interviews with entity staff.”
It follows a sequence of concentrate on audits performed by the auditor due to the fact 2013 that have uncovered major cyber resilience shortcomings, notably around the implementation of the leading 4.
But as with prior audits, the evaluate uncovered “maturity degrees for most entities were being drastically below” specifications under coverage ten of the protecting security coverage framework (PSPF).
Policy ten involves entities to achieve the maturity level ‘managing’, which the ANAO explained is equal to the essential 8 maturity level 3.
“Of the 18 entities assessed, only a person was rated as acquiring a running maturity level across all 8 controls,” the auditor explained.
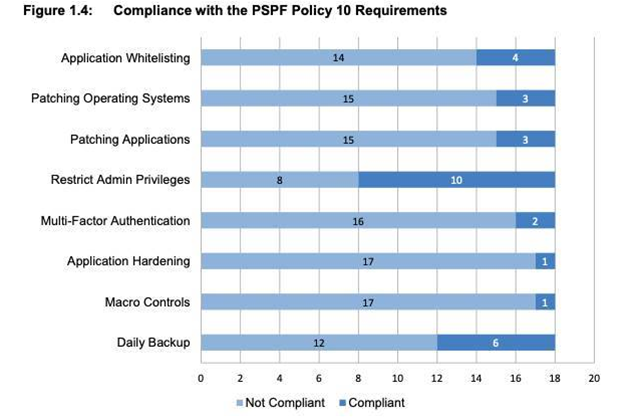
Source: ANAO
The evaluate uncovered the least expensive level of compliance related to the application hardening, macro controls and multi-issue authentication controls – all non-necessary under the essential 8.
“Achieving a Managing level for Application Hardening was considered by entities to be tricky thanks to the number of apps in the entities’ methods and the difficulty in identifying all applicable hardening controls,” the auditor explained.
But it also acknowledged that the the vast majority of agencies are organizing to tackle these fears by July.
“Entities have implementation strategies focused on lessening the number of apps in their environments, with an aim to lowering their assault surface area and minimising danger,” the ANAO explained.
“Implementation of these strategies is at this time becoming actioned by the the vast majority of entities, with most strategies scheduled for completion by July 2020.”
Limiting macros also differed widely involving agencies, with agencies reporting the management as tricky “due to consumers relying greatly on macros to conduct business activities”, with some relying on “additional mitigations” to tackle fears.
For Multi-issue authentication, agencies “found the method of organising/distributing multi-issue authentication tokens for all consumers to be an onerous one”, with most as a substitute accepting the danger and concentrating on acquiring a lesser maturity level.
“Entities prioritised multi-issue controls for remote entry and privileged consumers, relatively than all consumers,” the auditor explained.
The ANAO also uncovered that 4 agencies experienced incorrectly self-assessed, which the agencies blamed on a poor understanding of their specifications.
“The entities attributed the inaccuracies in their assessments to their interpretation of the scope of the requirement and indicated that they uncovered it hard to establish irrespective of whether they experienced satisfied the intention of the mitigation methods,” the report states.
Most entities were being also uncovered to have “conducted their self-assessment at a method or surroundings level and did not exclusively assess the controls demanded to minimise cyber pitfalls to their FMIS or HRMIS applications”.
ANAO assessment even worse than ACSC’s
ACSC’s current cyber security posture report to parliament uncovered most governing administration agencies were being however having difficulties to put into practice the essential 8 cyber security controls.
It explained seventy three percent of agencies claimed under baseline degrees of maturity with the necessary leading 4 controls previous calendar year, together with 13 percent who claimed advertisement hoc degrees of maturity.
Advertisement hoc is thought of the least expensive probable rating under the scoring metric, and indicates only “partial or essential implementation and management” of the leading 4.
But the auditor’s report indicates that factors are in reality even even worse than this.
“ANAO uncovered that seventy six percent of controls were being an advertisement-hoc or building maturity level,” the report states.
“This is in line with ACSC conclusions, which mentioned ‘73 percent of non-corporate Commonwealth entities reporting advertisement hoc or building degrees of maturity’.”
As this kind of, the auditor stressed “majority of the entities reviewed are not meeting the demanded Policy ten maturity level” and explained “significant progress was however required”.
The ANAO also pours cold drinking water on any recommendation that modifications to the PSPF in 2018 has led to any real improvement in cyber resilience.
This is in spite of the government’s cyber uplift in 2019, which assessed 25 agencies in the wake of the state-sponsored cyber assault towards Parliament House – Australia’s “first national cyber crisis”.
“The regulatory framework and self- assessments to day have not pushed the accomplishment of the common of cyber security demanded by Govt coverage,” the auditor explained.
“The coverage ten specifications, that non-corporate Commonwealth entities put into practice the ASD Required Approaches to Mitigate Cyber Security Incidents (Major 4), have been in put due to the fact 2013.
“Entities’ incapacity to meet up with these specifications indicates a weakness in implementing and retaining powerful security controls over time.
“Past audits of cyber security by the ANAO to assess the progress of implementation towards Policy ten specifications have not uncovered an improvement in the level of compliance with the controls over time.
“The work carried out as portion of this evaluate indicates that this sample proceeds, with minimal advancements.”
